-
Jon Galloway on new things in ASP.NET 5 and ASP.NET MVC 6
We’ve got another “big name international speaker” for ADNUG this month!
 Next week, we’re joined by Jon Galloway, a Microsoft Technical Evangelist based in San Diego, California. Jon will be speaking about the new features coming in both ASP.NET 5 and ASP.NET MVC 6. I assume we’ll see the final versions of these around the same time that Visual Studio 2015 ships.
Next week, we’re joined by Jon Galloway, a Microsoft Technical Evangelist based in San Diego, California. Jon will be speaking about the new features coming in both ASP.NET 5 and ASP.NET MVC 6. I assume we’ll see the final versions of these around the same time that Visual Studio 2015 ships.I first came across Jon through his being one of the presenters of the Herding Code podcast (I’ve been listening since 2009). More recently, I’ve watched some of his courses on Microsoft Virtual Academy, seen him appear weekly in the ASP.NET 5 Community Stand-ups and been following him on Twitter. He’s an engaging, knowledgeable, down-to-earth presenter and I’m anticipating it will be a great meeting.
If you’re in Adelaide, then please register and come along on Thursday 9th April at 12 noon, Microsoft Adelaide, Level 12, 147 Pirie St, Adelaide. Register via http://www.meetup.com/Adelaide-dotNET/events/221073867/
If you’re out of town or just can’t make it in person, then we’ll be running the session via a Google Hangout – so you can still participate in the live session or watch the recording after the event on YouTube.
Look forward to seeing you there in person or online 😀.
-
ALTER AUTHORIZATION
(For my own reference)
To resolve this issue in Microsoft SQL Server (often observed when you restore a database that came from another server):
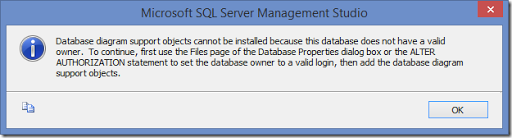
Run this:
alter authorization on database::[MyDbName] to sa;
-
MVA Figurines
In September last year, I took part in the MVA ‘Become a hero’ promotion. By signing up, I got a free t-shirt (and if you know me well, you’ll know that makes perfect sense). In addition by completing a number of online courses from the MVA site, you could then get a novelty figurine (or maybe up to 6 if you did more courses).
I received my t-shirt, but my figurine never arrived. It appeared the super powers of “DevOps Captain Code” also included the ability to get lost in the mail. “Oh well, at least I’ve got a t-shirt”, I thought.
But then yesterday I got home to discover two packages from Microsoft. One was another t-shirt (yay), and the other was the full set of 6 figurines.
So now we have (left to right)
- SQL Server Query Controller
- Azure Cloud Ninja
- Device Management Dr Device
- Windows Server Solid Server
- DevOps Captain Code
- Virtualisation Hypervisor
They’re now gracing my desk at work, much to the bemusement of my colleagues 😀
Figurines and t-shirts aside, if you’re after some quality free online training then there’s some excellent resources at the Microsoft Virtual Academy site. Most courses are run as a live event and then are made available on-demand a few weeks later (useful if the live event clashes with your preferred time to be asleep!)
